Information Sharing is a Linchpin for Securing Special Events
After the tragic events of 9/11, there was overwhelming consensus that a coordinated effort against terrorism and other public safety threats was required between the nation’s entire law enforcement, emergency management, and intelligence apparatus. This includes the identified requirement to secure large-scale public events. These events present a potential target for terrorism and other crimes based on size, scope, and especially notoriety.
As a result, National Special Security Event (NSSE) procedures were established in a portion of Presidential Decision Directive 62 in May 1998, which set out the security roles for federal agencies at major events. This was codified by law in the Presidential Threat Protection Act of 2000. The Department of Homeland Security (DHS) designates NSSEs based on the Special Event Assessment Rating (SEAR) to bring together the proper resources, expertise, and information sharing capabilities. Very few of the events evaluated garner the NSSE designation; most fall under SEAR event status with levels 1-5. These levels determine the amount of resources that the Department of Homeland Security (DHS) and other federal agencies will provide.
Regardless of designation, information sharing has rightly become an attribute of the highest priority in both the planning and response to events. How that information is shared, acted upon, and stored is a process that has made tremendous strides, but still continues to mature in scope and complexity.
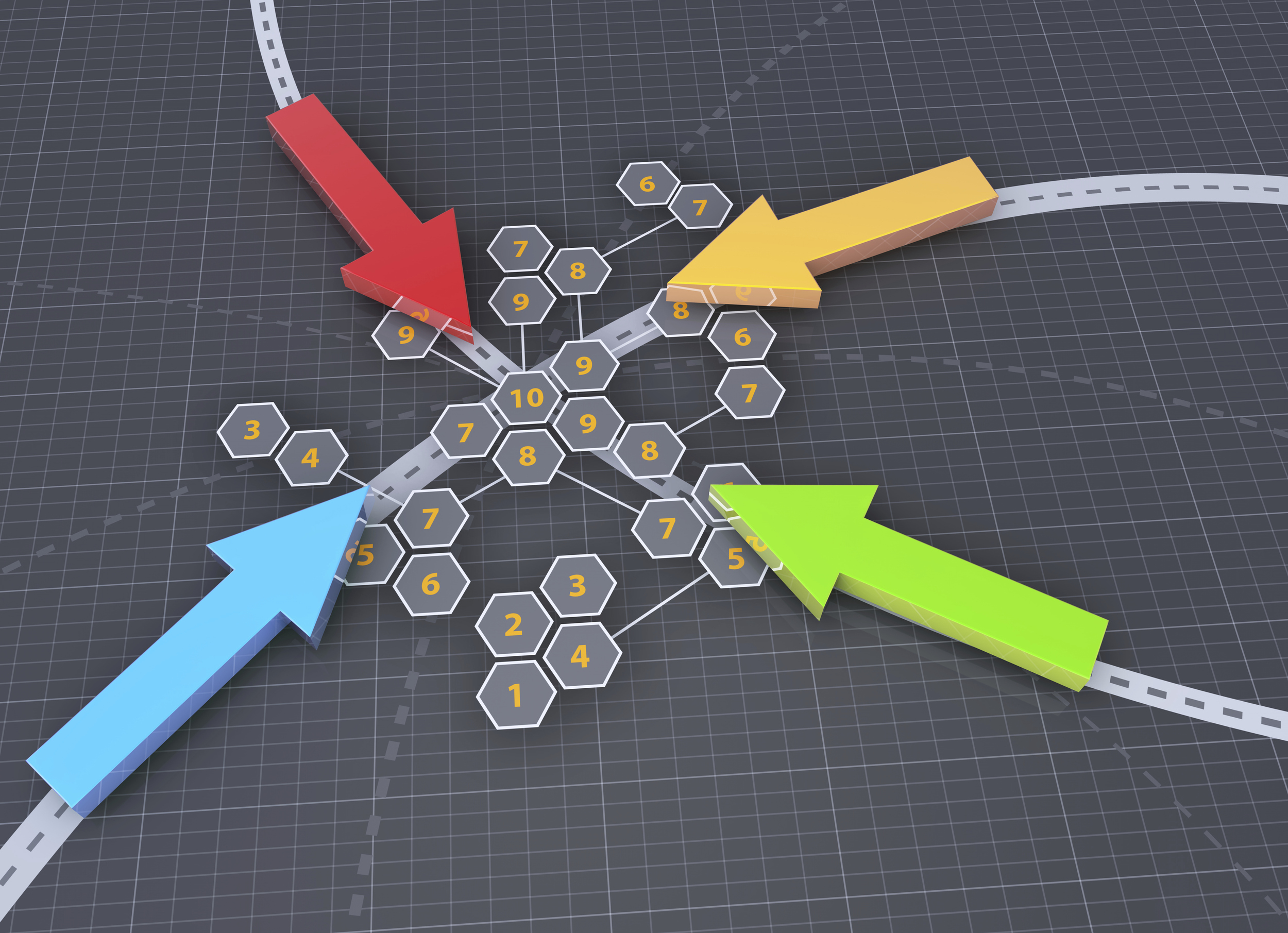
This need led to Multi-Agency Command Centers or MACCs at NSSEs and SEAR events. MACCs require representation from every jurisdiction and public safety domain involved with an event at the Federal, State, and Local level. That agency representative has the ability to share information instantly with the entire population of the MACC. They also bring the ability to reach back within their own agency for response, investigation, and follow-up. MACCs have become common place practice even in steady state communication centers and the role and scope of MACCs continues to evolve.
Bringing agencies together that share a common goal, but have different responsibilities and jurisdictions is challenging. The need to share information, task resources, and exploit expertise outweighs these challenges. Tragic criminal acts show that it is imperative for public safety officials to proactively share information which could endanger citizens.
Technology has also advanced the use of MACC principals in event security. Computer platforms help share information securely. Participants can now share information remotely from fixed locations or even at event sites via mobile devices with ease.
Sharing law enforcement and public safety information with those who have jurisdictional public safety missions is essential. Information sharing is a force multiplier that saves time, resources, and potentially even lives.
Learn more about how Arc Aspicio supports:
The Law enforcement Mission
The Emergency Management Mission
The Intelligence Mission





















