DNA:
The Last
Biometric
The integrity of the U.S. immigration system rests in the Department of Homeland Security’s ability to positively identify known and unknown individuals throughout the travel continuum. The travel continuum begins with the visa application process and continues through arrival at Ports of Entry, application for immigration benefits, investigation and removal of immigration offenders and exit from the host country. Collection of biometric information such as fingerprints, iris, and facial images has vastly improved the efficiency and accuracy of this often arduous identification process.
Moving Beyond Fingerprints
When the Department of Homeland Security (DHS) launched its US-VISIT program in 2003, it opted to use fingerprint biometrics to establish the identities of foreign nationals entering the U.S. It has since biometrically enrolled nearly 100 million foreign nationals. In this context, collection of fingerprints from foreign nationals has proven to facilitate legitimate travel while also enabling immigration officers to focus on potentially dangerous or threatening individuals.
The fingerprint alone, however, may not always offer sufficient information to establish an individual’s identity in an immigration and border management context. Some visa categories, for example, require applicants to establish biological relationships to sponsors in the U.S. In other cases, Immigration and Customs Enforcement agents may encounter foreign nationals with possible links to crime, but discover there are no latent fingerprints (i.e., the impression left by finger ridges invisible to the naked eye that is often found at the scene of a crime) on file with which to positively identify these suspected foreign criminals. Law enforcement authorities often use latent fingerprints to prosecute suspected criminals.
The fact that fingerprints alone may not fulfill the mission needs of DHS components operating in these particular circumstances has lead many experts to question the value of the use of biometrics. While these vulnerabilities may exist, it is important to note there are biometric complements to the fingerprint. DNA, for example can both establish a familial relationship and place a person at a crime scene where no latent prints exist.
DNA use in a border management and immigration environment may initially seem excessive and perhaps even unjustified. However, as DHS mission needs and ‘in scope’ immigrant populations evolve, DNA use may emerge as viable biometric of the future.
Figure 1 depicts the adoption of biometrics (left to right) in the mission-critical function of verifying the identification of individuals throughout the travel continuum – both in the U.S. and other countries around the world. Biometrics, such as fingerprints, facial recognition, and iris, are often used in combination to increase the accuracy of identifications.
Proven Use of DNA in the Immigration Environment
To reinforce the security, integrity and facility of the immigration system, DHS consistently researches emerging biometric identification technologies and their potential applications to identity management. One such biometric technology is DNA. Though some research suggests that because DNA testing is not an automated process, it is not a true biometric recognition system, both policy makers and scientists agree that the accuracy of DNA testing might result in future biometric applications.
DNA testing, in an ideal environment, requires at least four hours of processing. Always mindful of potential impacts to the efficiency of the immigration process, DHS recognizes that DNA testing is a viable option in limited benefits application cases where establishing biological relationships is a fundamental component of the adjudication process.
For example, the Priority Three Refugee Family Reunification Visa (P-3) requires applicants to demonstrate a biological relationship to a post-flight refugee legally residing in the U.S. After an eight month internal review of the P-3 application process, the Department of 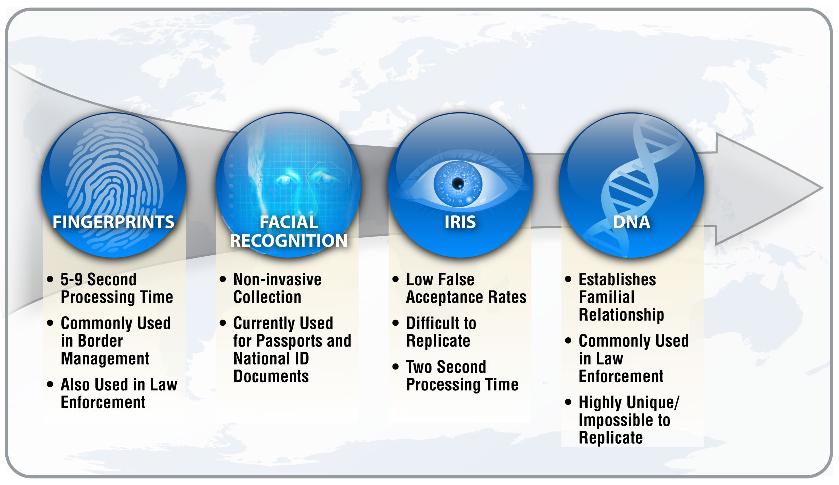 Figure 1 Biometrics enhance identity verification in a border management and homeland security context. DNA is an emerging biometric in this area.State and DHS jointly resolved to suspend applications to the P-3 visa category. A Department of State Fact Sheet, published in February 2009, concluded that in approximately 86 percent of the P-3 cases reviewed, individuals claiming to be family members either refused to take the DNA test or their DNA did not match that of their alleged relative.
Figure 1 Biometrics enhance identity verification in a border management and homeland security context. DNA is an emerging biometric in this area.State and DHS jointly resolved to suspend applications to the P-3 visa category. A Department of State Fact Sheet, published in February 2009, concluded that in approximately 86 percent of the P-3 cases reviewed, individuals claiming to be family members either refused to take the DNA test or their DNA did not match that of their alleged relative.
In an effort to bolster the integrity of the immigration benefits system, DHS’ U.S. Citizenship and Immigration Services (USCIS) anticipates continued collection of DNA from applicants where the Immigration Nationality Act (INA) requires that a legal relationship exist between the applicant and the US-based relative. Concerns surrounding applicant privacy, DNA database management and the integrity of overseas DNA testing centers will continue to affect adjudication outcomes in categories such as the P-3 Family Reunification Visa. While routine collection of DNA in a Port of Entry environment is unlikely due to processing constraints, it appears that DNA testing will continue to play a critical role in streamlining the immigration benefits process.
Could DNA Break the Code to Identity in Immigration Enforcement?
Future DNA use in a homeland security context may also extend to the immigration enforcement arena. In January 2009, the Department of Justice approved the collection of DNA samples from people arrested and detained for suspected immigration violations. Historically, immigration enforcement officers have collected fingerprints and photographs from suspected immigration offenders. However, as DNA studies demonstrate a 1-in-6-billion chance of two people having the same genetic profile, DNA might prove a valuable tool in prosecuting immigration violators with potential criminal histories.
DHS faces critical challenges as it seeks to minimize the compromise that often occurs between securing the nation and facilitating legitimate trade and travel. DNA has the potential to reduce visa processing times, prevent immigration fraud, and protect the U.S. borders and its interior when applied to an appropriate in-scope population and used in conjunction with more traditional biometric systems such as fingerprint, face recognition and iris.





















