Discount
Shopping
and Disaster
Response
In the spring of 2008, floods destroyed the water purification plant in Mason City, Iowa. Federal Emergency Management Agency (FEMA) personnel were not the first on the scene… Pepsi was. FEMA had set up an account with Pepsi to provide bottled water to the area until FEMA could arrive. This story shows how the Government and the private sector can effectively collaborate to quickly respond to and mitigate the impacts of disasters.
FEMA became part of the Department of Homeland Security in 2003. The agency is responsible for responding to state, local and tribal government’s requests for assistance when they cannot fully respond to disasters. After Hurricane Katrina in August 2005, the role of FEMA expanded significantly. Katrina placed FEMA into the spotlight and, with that, came more demand for help.
In response, FEMA has increased its emphasis on preparedness. However, FEMA is still called upon to respond to larger disasters. Both preparedness and response are areas where the private sector could aid FEMA.
Challenges
In early 2008, flooding devastated the Midwest and state and local governments asked FEMA to respond rapidly to support their disaster response efforts. While FEMA was quick to take action, the physical distance of the disaster areas from FEMA distribution centers limited their ability to quickly respond. FEMA currently operates five distribution centers in the continental U.S. – primarily in states on the southern border and the east coast, far from the heavily flooded Midwest.
This geographical problem becomes more complex in the absence of a single integrated tracking system. Supplies are normally shipped from a FEMA distribution center to federal operational staging areas (FOSAs). FEMA uses the Trading Partner Management (TPM) system to track items as they are shipped from distribution centers to the FOSAs. However, after the goods are received at the FOSA, FEMA personnel track items using paper forms or an improvised system called eFOSA.
The inability to track items from start to finish with an integrated tracking system results in a slower process, increased opportunities for fraud, and risks misplacing supplies.
However, the tracking problems actually start in FEMA’s distribution centers. FEMA uses a program called Warehouse Manager to keep an electronic inventory of supplies in a specific distribution center. According to a May 2008 OIG report, Warehouse Manager is only in place at two of FEMA’s five distribution centers. The other three distribution centers rely on improvised systems and paper tracking.
Solutions and Recommendations
The private sector is already in position to address FEMA’s challenges in both areas: infrastructure and logistics. Large retailers, such as Wal-Mart and Target, face many of the same issues that FEMA faces. Both groups must move large amounts of goods from distribution centers to specific staging areas and track those goods the entire way. By teaming with large retailers, FEMA can quickly, move vital resources – food, water, and clothing – to anywhere in the U.S. in the initial stages of a disaster.
In the case of the Midwest flooding, Target and Wal-Mart distribution centers in Northern Iowa, Illinois, Wisconsin, and Minnesota could have delivered immediate supplies to an area that FEMA would not be able to reach for days (Figure 1).
The private sector can also provide support in tracking supplies. In preparing for disasters, experts from private sector companies such as Fed Ex, Wal-Mart, and UPS, should help FEMA to create an integrated and comprehensive tracking and inventory system. These companies have faced the same problems that FEMA faces in identifying, moving, and tracking key supplies when rapidly responding to planned and unexpected changes in demand.
During a disaster, FEMA should utilize private sector logistics systems to help send material over greater distances more quickly and with more control. National transporters, such as UPS and FedEx, move large numbers of individual items daily to specific destinations around the country. By explicitly involving large retailers and logistics companies in preparedness plans and in response to specific disasters, FEMA can more rapidly and effectively respond to disasters anywhere in the United States.
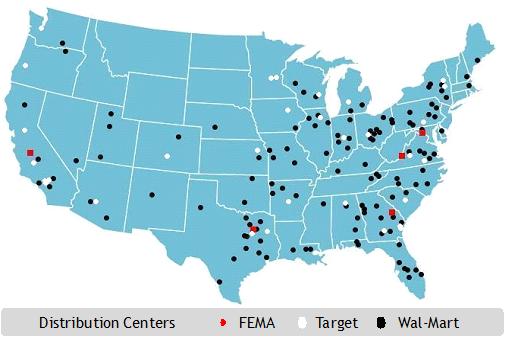 Figure 1 Distribution Centers of FEMA compared to Target and Wal-Mart.
Figure 1 Distribution Centers of FEMA compared to Target and Wal-Mart.





















